1 Introduction
Privileged Access Management (PAM) is an important part of access risk management and identity security in any organization. Privileged accounts have traditionally been given to administrators to access applications and services. But, changing business practices, hybrid IT, cloud and other aspects of digital transformation have meant that users of privileged accounts have become more numerous and widespread.
Privileged Access Management (PAM) solutions are critical cybersecurity controls that address the security risks associated with privileged access in organizations. Traditionally, there have been primarily two types of privileged users.
Privileged IT users who need access to the IT infrastructure supporting the business. Such permissions are usually granted to IT admins who need access to system accounts, software accounts or service accounts.
Privileged business users who need access to sensitive data and information assets such as HR records, payroll details, financial information or intellectual property, and increasingly, social media accounts.
Further digital transformation, regulations such as GDPR, cloud infrastructure and, most recently, the growth of DevOps in organizations looking to accelerate their application development processes are all adding to the growth of PAM
The reason for this mini boom in PAM deployment is that these trends have triggered an explosion in data and services designated as business critical or confidential, with a concurrent rise in the number of users and applications that need to access them. CISOs and IT chiefs realised that without dedicated solutions to manage these, the organizations would be at greater risk of hacks and security breaches. Cyber criminals have long targeted unprotected privileged accounts as one of the easiest routes to get inside an organization to steal data or damage infrastructure.
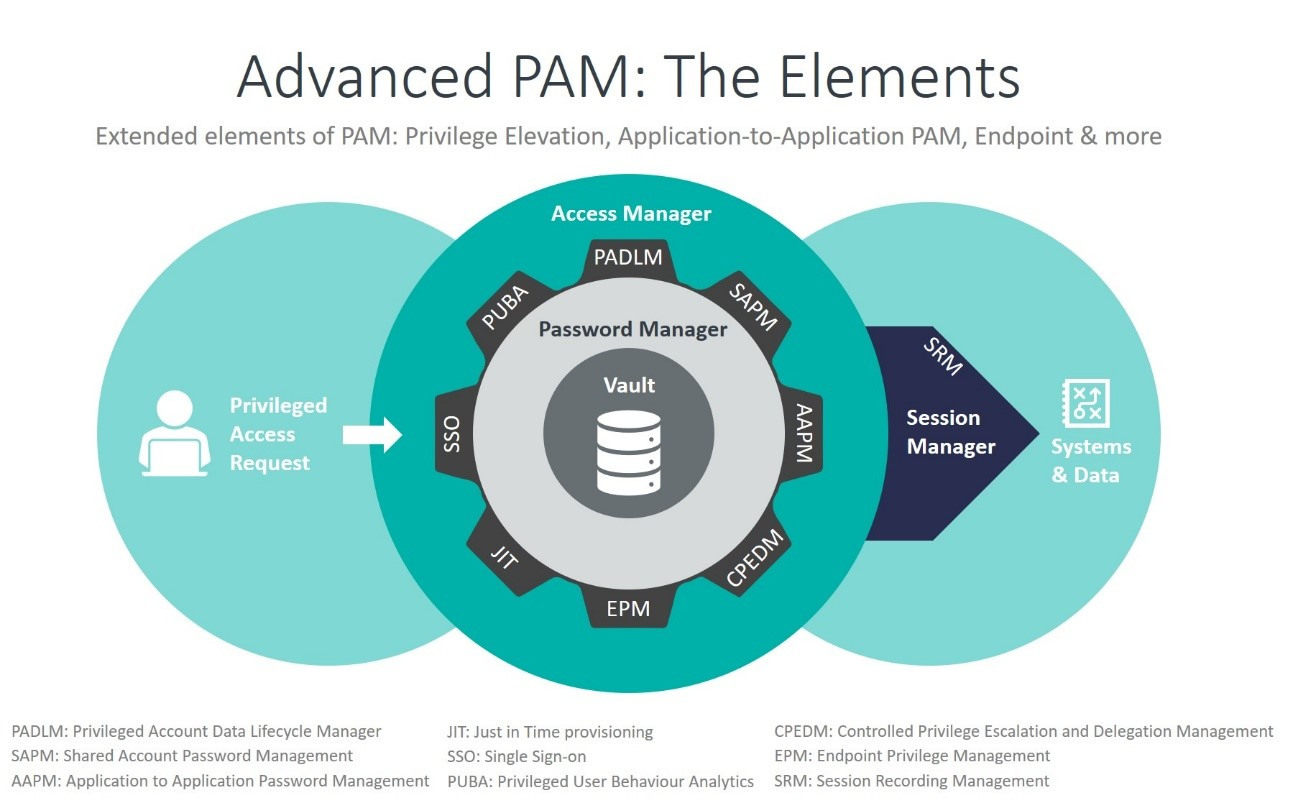
In recent years, PAM solutions have become more sophisticated, making them robust security management tools in themselves. While credential vaulting, password rotation, controlled elevation and delegation of privileges, session monitoring are now almost standard features, more advanced capabilities such as privileged user analytics, risk-based session monitoring, advanced threat protection, and the ability to embrace PAM scenarios in an enterprise governance program are becoming the new standard to protect against today's threats. Many vendors are integrating these features into comprehensive PAM suites while a new generation of providers are targeting niche markets such as PAMaaS or PAM for DevOps